CSA STAR Certification vs. CSA STAR Attestation
In the popular modern musical Hamilton, the titular character is given an opportunity by George Washington. Hamilton can stay on the front lines of the American Revolution, or he can become the general’s aide-de-camp. It’s a choice between gaining glory amidst the fighting or an office job with an opportunity to influence who would become our first president.
There really wasn’t a wrong choice for Hamilton to make, though he eventually chose to stay with Washington, become our first Secretary of the Treasury, and have a major Broadway production written about his achievements and life. (Seems it all worked out.)
When it comes to the CSA STAR Program, it’s the same sort of thing. There are two options, both of which offer benefits and drawbacks—if you’re a cloud service provider (CSP), it’s just a matter of figuring out which road suits your organization the best (if any).
But just like it was for Hamilton, it can be a difficult choice. That’s why, in this article, we’re going to make it a little easier for you.
As one of the only firms authorized to provide both CSA STAR Certification and Attestation services, we’re going to provide an overview of each, along with the pros and cons. With such valuable insight gained, you’ll be able to inform and simplify your approach to this program.
What is CSA STAR Certification?
Let’s begin with certification. Obtaining it means undergoing a third-party independent assessment that leverages the requirements of the ISO/IEC 27001:2013 (ISO 27001) management system standard together with the CSA Cloud Controls Matrix (CCM) version 4.0.
To even get started here, you must:
- Have an active ISO 27001 certification: or
- Be actively performing a STAR Certification assessment in tandem with an ISO 27001 initial certification review.
The certification assessment includes an evaluation of your maturity level across each CCM security domain, of which there are 17. The maturity level of each domain is scored from 1 to 15 based on your standing at that point in time:
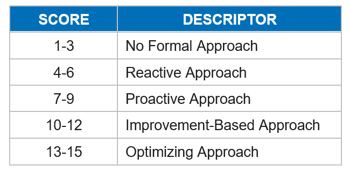
The lowest score for any given control in a domain is the score for that domain, which is then averaged, against all domains to yield your overall maturity score. That will determine whether you receive no award, a bronze award, a silver award, or a gold award in your CSA STAR report. (However, if you receive an award, it will not be included on your CSA STAR certificate.)
Having successfully achieved certification, you’ll be able to register on the CSA STAR Registry.
The Pros and Cons of CSA STAR Certification
CSA STAR Certification Benefits
- Complements your ISO 27001 certificate
- An active ISO 27001 certificate communicates that you have a security program in place that helps to identify, mitigate, and monitor information security risk within your management system.
- The additional CSA STAR certificate provides further reassurance to customers and business partners that you have established a base maturity level in managing the internal operations relevant to the 17 different security domains in the CCM.
- Additional opportunities for security enhancement
- The assessment required for certification can identify further improvements to your management system and approach to the CCM security domains so that you can eventually increase your overall maturity level and provide further assurances.
CSA STAR Certification Drawbacks
- ISO 27001 certification prerequisite
- As mentioned before, you have to already have ISO 27001 certification or, at the very least, you must be in the process of attaining it if you’re seeking to start the CSA STAR Certification process. This requires more time and more money to facilitate.
- Focus on maturing processes relevant to the CCM, rather than controls
- Formal control testing is not required for the CSA STAR Certification.
- Lack of details in the deliverable
- Similar to ISO 27001, you'll get the certificate. There's also a formal, internal report that's not publicly available, but you can provide it to customers if you choose; however, while it will communicate the compliance and “process” effectiveness of the management system, it does not contain relevant testing and results.
What is CSA STAR Attestation?
If you’re looking for another option, the STAR Program also features the CSA STAR Attestation. Like the certification, this is a third-party independent assessment of your security, but rather than drawing from ISO, the STAR Attestation uses the SOC 2 framework together with the Cloud Control Matrix (CCM).
Unlike the certification, the STAR Attestation does report on the design and operating effectiveness of your controls relevant to the applicable TSPs (which can include Security, Availability, Confidentiality, Processing Integrity, and Privacy) and the criteria in the CSA CCM.
The latter includes 17 security domains listed below:
- Audit and Assurance
- Application and Interface Security
- Business Continuity Management and Operational Resilience
- Change Control and Configuration Management
- Cryptography, Encryption, and Key Management
- Datacenter Security
- Data Security and Privacy Lifecycle Management
- Governance, Risk, and Compliance
- Human Resources
- Identity and Access Management
- Interoperability and Portability
- Infrastructure and Virtualization Security
- Logging and Monitoring
- Security Incident Management, E-Discovery, and Cloud Forensics
- Supply Chain Management, Transparency, and Accountability
- Threat and Vulnerability Management
- Universal Endpoint Management
To assess your controls as such, the evaluation takes place over a review period typically no less than six months.
Benefits of a CSA STAR Attestation
- No prerequisites
- Despite that, it’s recommended that you perform a pre-assessment to help identify gaps in the requisite controls before the start of your defined review period.
- You’ll better understand the criteria, as well as the commitments and system requirements as objectives of said applicable criteria. A pre-assessment will also help you identify risks and devise controls to mitigate that risk.
- A detailed report that can be provided to customers or potential customers
- The CSA STAR Attestation report includes a narrative of your system, the applicable criteria, control activities, and the service auditor tests applied, as well as test results.
- This stand-alone report highlights the granularity of your controls and can provide reliance on those controls that were operating effectively during your defined review period.
- Prescriptive criteria in the TSPs and CCM
- That means that your customers will be able to evaluate one CSA STAR Attestation report to another and have a common comparison between the two as both were assessed against the same criteria.
Drawbacks to a CSA STAR Attestation
- Disclosure of findings
- Any exceptions identified during the assessment will be noted in your report. So, if a control was not operating effectively during the review period, the results of that testing must be disclosed.
- Regressive results (not necessarily forward-thinking)
- As opposed to the CSA STAR Certification, which allows you to demonstrate an active management system that addresses, mitigates, and monitors information security risk, the Attestation provides the operational results of controls that already occurred.
- So yes, the report is meant to be relied upon but it’s not actively relevant after the review period has ended.
Next Steps for Your Organization and the CSA STAR Program
Now that CSPs have the opportunity to undergo third-party assessments against the CCM, you now have a choice—the STAR Certification or STAR Attestation program. Both hold value and can boost your assurance to your customers, but like Alex Hamilton made his pivotal choice way back when, you too need to decide which direction suits your needs—just like Ham did.
The good news is that you’ve got the information to do that now, though we understand you may still have some lingering questions. If that’s the case, please reach out to us so that we can address any concerns and make your decisions around this program easier.
In the meantime, you may want to consider other options for your cloud security. Check out our other articles addressing other standards that can help:
About RYAN MACKIE
Ryan Mackie is a Managing Principal at Schellman, and has been with the firm since 2005. Ryan supports the regional Florida market and manages SOC, PCI-DSS, ISO, HIPAA, and Cloud Security Alliance (CSA) STAR Certification and Attestation service delivery. He also oversees the firm-wide methodology and execution for the ISO certification services, including ISO 27001, ISO 9001, ISO 20000-1, and ISO 22301 as well as CSA STAR certification services. He has over 25 years of experience. Ryan also is an active member of the CSA and co-chairs the Open Control Framework committee which is responsible for the CSA STAR Program methodology and execution.




